From 28 April 2026, Cyber Essentials v3.3 introduces a requirement that changes who owns cyber security inside your organisation.
That single change moves Cyber Essentials from an IT exercise to a governance commitment.
If you are a Managing Director, Finance Director, Operations Director or trustee, this affects you directly.
What Changes in Cyber Essentials v3.3 from April 2026?
The key change is this:
A director must confirm the organisation will maintain compliance with Cyber Essentials controls for the full certification period, not only at the point of assessment.
This is not a cosmetic update.
It alters accountability.
Previously, Cyber Essentials often operated as a snapshot. Controls were reviewed. The questionnaire was completed. Certification was granted.
Now the declaration requires leadership to confirm that controls will remain in place and effective over time.
That means:
- Scope must be clearly defined
- Access control must be actively managed
- Security updates must be consistently applied
- Remote and cloud environments must remain protected
- Compliance cannot drift between renewals
This shifts the conversation from configuration to governance.
Why the Director Sign-Off Matters
The most important word in the new requirement is not “director”.
It is “maintain”.
Maintaining compliance requires structure, ownership and oversight.
Consider what can happen in a typical SME over 12 months:
- A new cloud system is introduced and not added to scope
- An employee receives administrative rights that are never reviewed
- Devices miss updates due to remote working
- A supplier retains access long after a project ends
- A personal device connects to corporate email without proper controls
None of these scenarios require sophisticated attackers.
They are operational drift.
The director declaration exists to prevent that drift.
It requires leadership to be confident that controls are not only implemented, but sustained.
Cyber Essentials v3.3 Is No Longer an IT Checklist
Cyber Essentials still focuses on five technical control areas:
- Firewalls
- Secure configuration
- User access control
- Malware protection
- Security update management
Those pillars remain.
What has changed is accountability.
Technology teams implement controls.
Leadership must ensure they are governed.
This is the difference between:
“IT says we’re secure.”
and
“We can demonstrate that our controls are maintained.”
The second statement is a governance position.
Why Cyber Security Has Moved Into the Boardroom
Cyber risk today is business risk.
When a cyber incident occurs, the impact rarely stops at systems.
It affects:
- Revenue
- Contracts
- Regulatory exposure
- Reputation
- Insurance
- Operational continuity
For SMEs, the operational disruption can be severe.
Many incidents are not caused by complex exploits.
They begin with:
- Weak or reused credentials
- Missing security updates
- Excessive administrative access
- Unmanaged remote devices
- Cloud misconfiguration
Cyber Essentials was designed to address these common weaknesses.
Version 3.3 reinforces that preventing them requires governance discipline.
What Directors Should Be Asking Now
If you are required to sign the Cyber Essentials declaration, you should expect clear answers to practical questions.
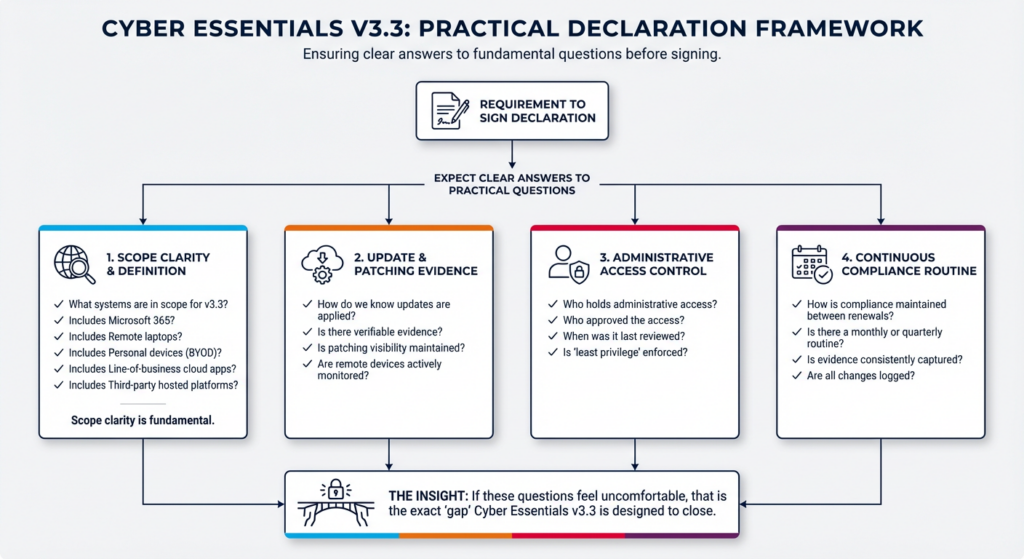
1. What systems are in scope for Cyber Essentials v3.3?
Does this include:
- Microsoft 365?
- Remote laptops?
- Personal devices used for work?
- Line-of-business cloud applications?
- Third-party hosted platforms?
Scope clarity is fundamental.
2. How do we know updates are being applied?
Is there evidence?
Is patching visible?
Are remote devices monitored?
3. Who has administrative access?
Who approved it?
When was it last reviewed?
Is least privilege enforced?
4. How do we ensure compliance is maintained between renewals?
Is there a monthly or quarterly routine?
Is evidence captured?
Are changes logged?
If these questions feel uncomfortable, that is the gap Cyber Essentials v3.3 is trying to close.
The Risk of Treating Cyber Essentials v3.3 Certification as a One-Off Event
Many organisations approach Cyber Essentials reactively.
Preparation begins shortly before renewal.
Evidence is gathered.
Settings are checked.
Compliance is achieved.
Then attention moves elsewhere.
The new declaration discourages that cycle.
Because leadership must confirm ongoing compliance, Cyber Essentials becomes a year-round discipline.
This aligns more closely with governance-led frameworks such as ISO 27001.
The direction of travel is clear:
Cyber Essentials is evolving from a checklist into a structured baseline of cyber governance.
Common Ways Organisations Drift Out of Compliance With Cyber Essentials v3.3
The most frequent causes of Cyber Essentials issues are operational, not technical.
- Scope drift when new systems are added
- Admin access creep during busy periods
- Missed updates on a subset of devices
- Remote working exceptions becoming permanent
- Supplier access without review or time limits
These are governance weaknesses.
They require process and ownership.
Not simply more tools.
What “Maintain Compliance” Looks Like in Practice
Maintaining compliance is about rhythm.
It means:
- Defined scope documentation
- A responsible owner for Cyber Essentials
- Routine update monitoring
- Scheduled access reviews
- Clear device standards
- Logged exceptions with remediation timelines
It is about making security visible to leadership.
When that structure exists, director sign-off becomes a statement of confidence rather than exposure.
Why The Cyber Essentials v3.3 Changes Matter for SMEs
Large enterprises have dedicated cyber security teams.
Most SMEs do not.
In many organisations:
- IT is outsourced
- Operational staff wear multiple hats
- Governance processes are informal
That environment makes drift more likely.
Cyber Essentials v3.3 raises expectations for SMEs without making controls more complex.
It simply expects organisations to treat cyber security as an operational discipline.
That requires leadership engagement.
Cyber Essentials v3.3 and the Direction of UK Cyber Policy
This change aligns with wider UK expectations around accountability.
Across sectors, regulators increasingly expect boards to understand and oversee cyber risk.
Insurance providers are tightening controls.
Supply chains require evidence of compliance.
Government contracts demand baseline standards.
Cyber Essentials is becoming a trust signal.
The director declaration strengthens that signal.
It demonstrates that security is not delegated and forgotten.
It is owned.
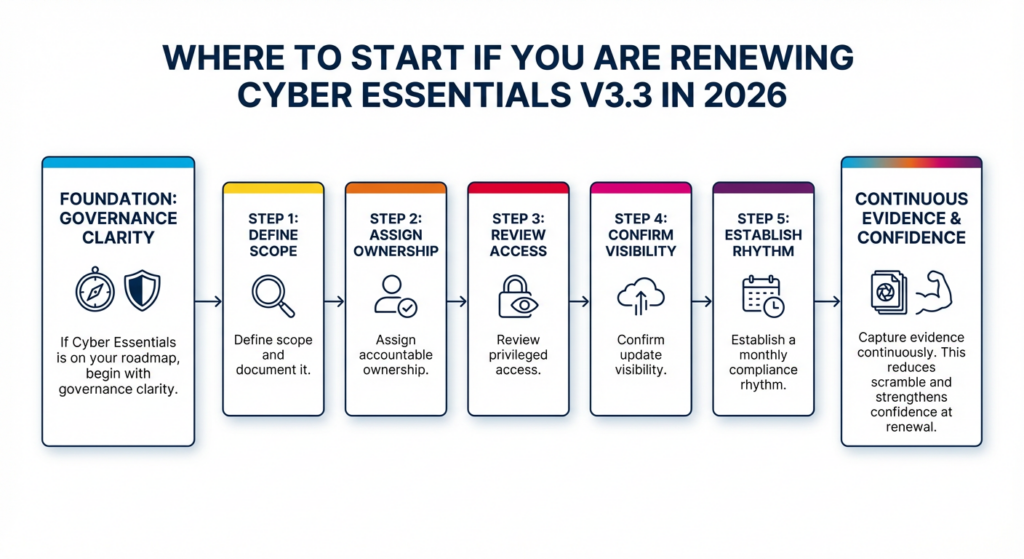
Where to Start if You Are Renewing Cyber Essentials v3.3 in 2026
If Cyber Essentials is on your roadmap, begin with governance clarity.
- Define scope and document it.
- Assign accountable ownership.
- Review privileged access.
- Confirm update visibility.
- Establish a monthly compliance rhythm.
- Capture evidence continuously.
This reduces scramble and strengthens confidence at renewal.
The Bigger Picture
Cyber Essentials began as a practical technical baseline.
Version 3.3 reinforces something many leaders already understand.
Technology does not create security.
Governance does.
By requiring director-level confirmation of ongoing compliance, Cyber Essentials recognises that cyber risk belongs alongside financial and operational risk.
In the boardroom.
Frequently Asked Questions
What changed in Cyber Essentials v3.3?
From 28 April 2026, a director must confirm the organisation will maintain Cyber Essentials compliance throughout the certification period. BondgateITMarketing
Why does the director sign-off matter?
It shifts accountability from IT alone to board-level governance, requiring leadership to ensure controls are maintained, not just implemented.
Does this make cyber security a board responsibility?
Yes. The declaration formalises leadership accountability for maintaining cyber security controls.
What does “maintain compliance” mean?
It means keeping required controls in place between certification and renewal, including updates, access management, secure configuration and device protection.
Who should sign the declaration?
A director, trustee, board member or equivalent senior officer with authority over organisational risk.
What is the biggest risk to compliance?
Operational drift — new systems added without review, admin access creep, missed updates, unmanaged remote devices, and undocumented exceptions.
Final Thought
Cyber Essentials v3.3 is not simply an update to wording.
It is a signal.
Cyber security is no longer something that sits quietly in IT.
It is a leadership responsibility.
And from April 2026, it is one that must be formally confirmed.
